Kubernetes - Restrict API server access by IP address
Restrict access to the Kubernetes API server by IP address.
On this page
The Kubernetes API server is a highly privileged system and should be secured. If you have a VPN available, you should restrict access to the API server by configuring firewall rules to only allow traffic from your VPN’s IP address.
When attempting to access a Kubernetes API server that has restricted access by IP enabled, traffic not originating from a listed IP will be denied access.
Configuring IP restrictions
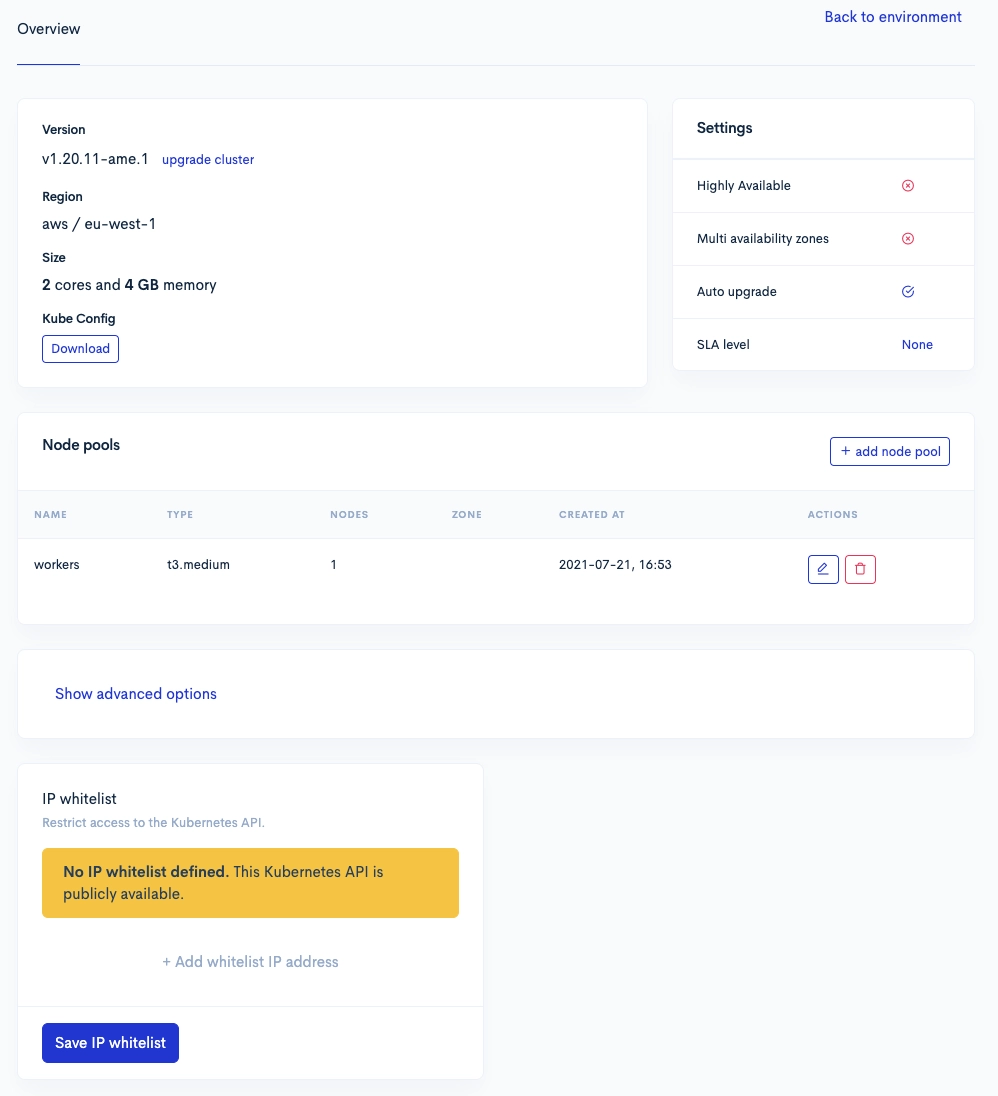
When you open the cluster’s detail page, you can get an overview of all settings available. On the bottom is the option to restrict access to the Kubernetes API server.
You can configure any IPv4 CIDR address block in here.
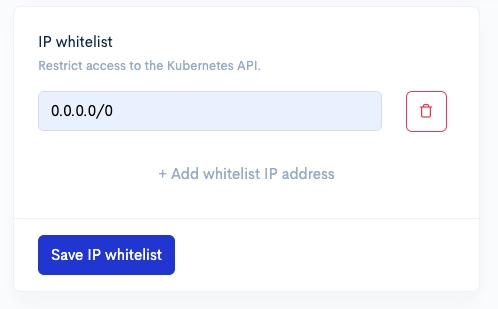
When you configure a new CIDR range, press the save button below. The configuration for the API server will update in the background. This process usually takes between one and three minutes.
Notes
- Anyone attempting to access a restricted API server from a different IP range will receive an access denied.
- You can configure up to 10 CIDR ranges per API server.
- Traffic coming from your cluster is allowed even if it’s CIDR range is not configured.